Blog
Security of In-App Mobile Advertising
By TrustGo Security Labs On February 1, 2012 In Security
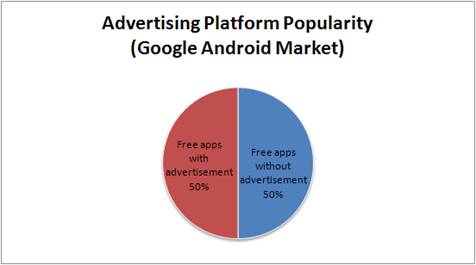
In-app mobile advertising grew explosively in the year 2011 as more and more mobile apps were developed, and it’s now projected to be at least a $2 billion industry. Just how popular is it? In Google’s Android Market, 50% of all free apps communicate with at least one mobile advertising network.
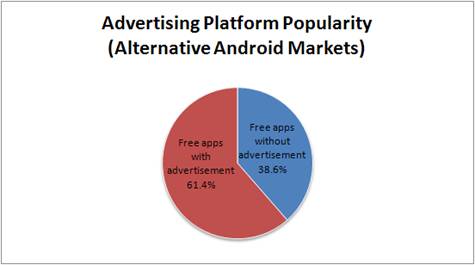
If we look at the alternative markets alone, the percentage is higher, with nearly two-thirds (61.4%) of apps containing mobile ads.
In-app mobile advertising indeed brings money to app developers, which easily explains the numbers above. For the user, beyond being a source of minor annoyance, it may also be a security and privacy risk.
We recently analyzed more than 100 in-app mobile advertising platforms on Android, and found that a large portion of advertising platforms have security, privacy and usability issues.
Here are some of the issues we identified:
Privacy leaks
Mobile advertising is a big threat to a user’s privacy. We observed that 88% of mobile advertising platforms leaked information–in clear text–that could be used to identify the user or device, such as the IMEI, IMSI, etc.
28% of the mobile advertising platforms leaked the user’s phone number; these platforms are currently embedded in about 36,000 Android apps worldwide, which have been downloaded more than 1.3 billion times in total.
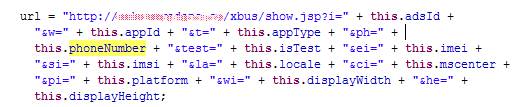
Most of the advertising platforms send the user’s phone number to their website via an HTTP GET method when retrieving advertisements. Here is a URL used by one of the platforms for getting advertisements (phone number in red):
ad.xxxxxx.com/ad/?t=1&v=1.0&s=4&sv=1&uid=000000000000000&id=XNZDYYYY&tm=100&fm=100&m=sdk&loc=zh-CN&gps=0%2C0&bas=0&lac=0&imsi=310260000000000&sc=15555218135&w=320&h=50
Code snippet from another platform:
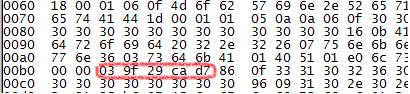
Some of them send the phone number in binary format via an HTTP POST method:
Installing apps without confirmation
Mobile advertisements are sometimes used for app promotion. When these ads are clicked, the user will be redirected to a download page, or an application will be downloaded automatically without clear notice.
30% of mobile advertising platform have this type of advertisement. Of those, 70% directly download an application package, instead of using Android Market. Downloading the application directly is a huge security risk. Since the app being downloaded is provided by an advertiser, instead of a trusted source, malicious advertisers can easily use this method to distribute malware. This technique has already been used by some malware, such as the “GGTracker”, which was discovered in June 2011.
Texting without confirmation
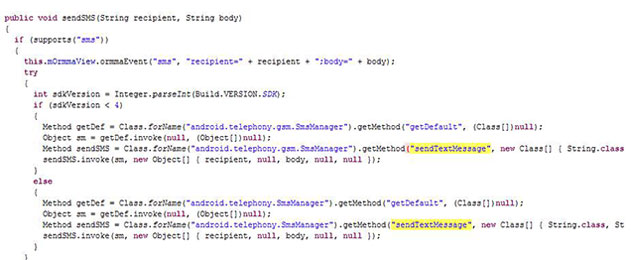
Fortunately, the practice of sending unsolicited text messages is not yet as widespread, though we still found some perpetrators. For example, one of the platforms provides a JavaScript file for the advertiser to embed in their web page. This JavaScript contains code to directly send a text message through the Android Java sendTextMessage() API.
JavaScript code:
Java code:
Since the web content is controlled by the advertiser, the advertiser is able to control whether a message is sent, as well as what’s included as message content.
Calling phones without confirmation
Some advertising platforms induce the user to make a phone call to the advertiser. These platforms make the calls in two different ways: by bringing up the system dialer UI, or by calling the number directly.
Among those platforms making phone calls directly, we found that only one of them makes phone calls without user confirmation, while all the others will show a dialog before the call is actually made.
Creating advertisement shortcuts on the desktop
Some applications add a shortcut linked to the advertiser’s website without the user’s awareness.
Writing text messages directly to the inbox
We found that one of the advertising platforms writes advertisements directly to the user’s SMS inbox, which tricks the user into thinking that he/she has just received a message from a trustworthy sender.
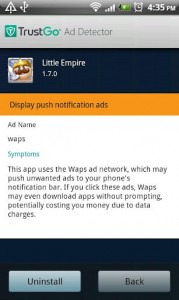
Notification ads
Some advertising platforms can push ads to the user’s phone, usually appearing in the notification bar. The push features are commonly implemented using an Android service. Once started, the service will be always running, even if the user exits the app. Some applications will even configure the service to start automatically at each system boot.
We believe that uncovering these security and privacy issues surrounding in-app mobile advertising is important for both mobile end-users, as well as developers. As a user, without awareness of these threats, your identity and personal data could be at risk. For developers, it means that an app you write may be collecting sensitive data or performing other malicious tasks on behalf of your advertiser, without the awareness of you or your customers.
Here are some suggestions for mobile users:
- Do not click links or banner ads unless you are very sure about the content. Never install apps directly from in-app ads or advertisers’ websites. Instead, get apps from the Android Market, or use the TrustGo Mobile Security / TrustGo Mobile Search apps to find and download trusted apps from over 30 Android markets worldwide.
- TrustGo provides AD Detector app. Ad Detector detects a slew of potential privacy violations and identity leaks, including newly found malware Apperhand. It’s an easy way to see which apps may be doing dangerous things behind your back. Once detected, with just one click, you can remove these apps from your mobile device
https://play.google.com/store/apps/details?id=com.trustgo.addetector


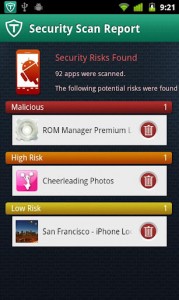
- To keep your identity and your mobile device safe, we strongly recommend installing the TrustGo Mobile Security app, which provides everything you need to guard against not just risky advertisements, but also malware, viruses, and other privacy threats.
https://play.google.com/store/apps/details?id=com.trustgo.security

If you’re developing an Android app, here are some recommendations:
- Carefully choose your advertising platform. Be sure you fully understand its behavior before integrating it into your code.
- Remember that virtually none of your users will understand the distinction between your app and the ad platform, so any security issue encountered will hurt the reputation of your app and your brand.
- If you’re unsure about a particular advertising platform, feel free to email us, and we’ll be happy to share more detailed information.